
Written by Nic Cline, ICS Consulting Manager, North Texas
Cybersecurity: A Shared Responsibility
Securing critical infrastructure isn’t just about having the right technology—it’s about having the right approach. Leadership and operations both play a crucial role in ensuring that cybersecurity isn’t just a box to check, but a core part of business continuity and risk management.
The challenge? Many organizations are focused on keeping systems operational, managing budgets, and maintaining efficiency. Cybersecurity can sometimes feel like an extra burden rather than a critical priority—until an incident forces immediate action.
At RED Group, we’ve worked with organizations that do an incredible job maintaining operations but may not always have visibility into the risks in their digital infrastructure. In some cases, vulnerabilities go unaddressed until disruptions occur, requiring urgent action. But the best security strategies are proactive, not reactive.
The Risks of Waiting Until Action is Mandated
Consider this scenario:
A municipal organization overseeing critical infrastructure had internet-facing components with minimal security controls. While the team was highly skilled in managing daily IT and OT operations, cybersecurity wasn’t their primary focus. Over time, as threats evolved, their exposure increased—but risks were not mitigated.
Eventually, the situation escalated. Due to the potential risk, federal agencies suggested immediate security measures. While the organization adapted quickly, addressing the vulnerabilities earlier would have minimized risk and provided more time for strategic implementation.
This example isn’t unique. Across industries, organizations face similar challenges balancing operational priorities with evolving cybersecurity needs. The key is ensuring security doesn’t become an afterthought—it should be integrated into everyday decision-making.
How Leadership Can Drive Proactive Cybersecurity
Leadership teams set the tone for cybersecurity culture. A strong, proactive security strategy starts with prioritizing risk management, compliance, and long-term resilience. Here’s how leadership and operations can align to build a stronger security posture:
- Make Cybersecurity a Business Priority – Security isn’t just an IT issue; it’s a core part of operational resilience. Integrating cybersecurity into business strategy ensures long-term protection.
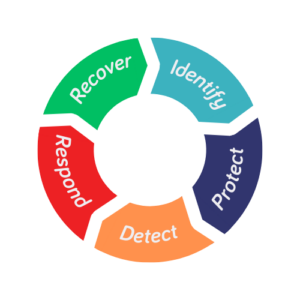
- Stay Ahead of Regulatory Requirements – Agencies like DHS and CISA are tightening security expectations. Proactively adhering to sector-specific risk management frameworks avoids last-minute compliance challenges.
- Invest in Strategic, High-Impact Security Measures – Firewalls, network segmentation, and continuous monitoring are cost-effective first steps that provide significant protection.
- Empower Your IT and OT Teams – Give teams the resources and training they need to identify and address vulnerabilities before they become critical issues.
- Foster a Culture of Collaboration – Cybersecurity is most effective when leadership, IT, and operations work together to identify risks and implement solutions.
A Smarter Approach to Critical Infrastructure Security
At RED Group, we believe that cybersecurity should be an integrated, strategic initiative—one that supports operational success rather than disrupts it. With the right approach, leadership and operations can work together to strengthen security, improve compliance, and protect critical infrastructure before risks turn into mandates.
Want to take a proactive approach to securing your infrastructure? Let’s talk. Schedule a consultation today and take proactive steps to strengthen your infrastructure security with confidence.
Nic Cline, ICS Consulting Manager of RED Group’s North Texas office, has over 18 years of experience in Automation, Controls, and Robotics. He has spent the past nine years working in North Texas’s Water/Wastewater industry, leading SCADA and controls projects and overseeing engineering management, technology strategies, and company growth initiatives.





Recent Comments